People are hacking diabetes pumps — and that’s both bad and good
BLOG: Heidelberg Laureate Forum

When two computer scientists discovered a vulnerability in a popular insulin pump, they were understandably concerned. It was a serious problem: an attacker could withhold insulin from the user, or even worse, deliver a large, potentially fatal dose. They tried reaching out to the producer and regulators, but six months later, there was no change. That’s when they decided to take matters into their own hands and build an app that could kill people.
This article is the second in our ongoing series about hacking and IoT. The first article can be found here:

According to the World Health Organization, about 80 million people need regular injections of insulin — everyone with Type 1 diabetes, and about a fifth of those with Type 2 diabetes. About half of those can’t afford the treatment or don’t have it available where they live. Even for the ones who can afford it, the treatment can be very challenging, which is why insulin pumps can be a godsend.
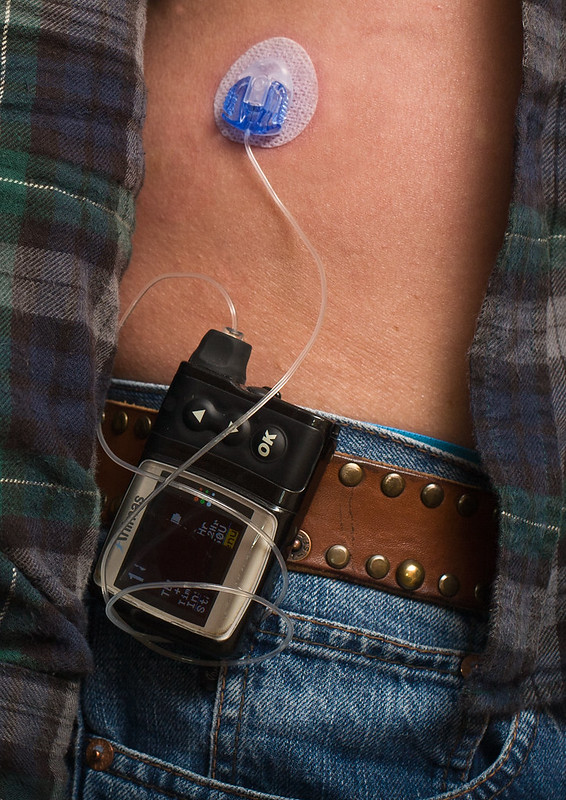
Instead of going to the hospital regularly for injections, insulin pumps essentially deliver continuous subcutaneous treatment. You put an infusion set on your belly, a glucose sensor, and a smart device that controls the pump and you’re good to go, no hospital required.
Insulin pumps offer patients much-needed autonomy and enable them to go about their life in a fairly normal fashion. But what happens when these devices can be hacked?
Black hat hacking
A 2016 study found that in the US alone, there were over 350,000 users, and the number has been continuously on the rise. Some systems are more complex and feature multiple sensors and wireless connectivity that can track blood sugar levels, while others require constant monitoring. But many of them can be hacked.
Concerns about diabetes pumps blew up in 2011, when an IBM researcher by the name of Jay Radcliffe, demonstrated a security flaw in insulin pumps. Radcliffe, a diabetic himself, was able to hack the wireless interface of his own pump and control it remotely. He would then go on to continue his research in hacking objects, noting that “emerging technologies are often ill-equipped” for the dangers of an interconnected world. Turns out, he was right.
Just a few years later, research from McAfee found another vulnerability in diabetes pumps, and concerns continued to loom. But things really took a bizarre turn in 2017 when two security experts (Billy Rios and Jonathan Butts from QED Secure Solutions) found a major vulnerability in thousands of insulin pumps.
The two tried to discuss with both authorities and the pumps’ producers, but little changed. The company producing the pumps warned its customers of the vulnerability, but this made little difference and the problem wasn’t fixed. Annoyed that they weren’t being taken seriously, they presented their finds at one of the biggest hacking conferences: Black Hat Briefings, in Las Vegas. It worked: their talk went viral and was widely publicized, and for good reason.
The two essentially created a “master key” for a type of insulin pump — a remote that could take the devices over and do as the attacker pleases. All the attacker would need to know is the insulin pump’s serial number, but even this could be brute-forced by trying combinations over and over again. Then, it was relatively easy to determine the radio frequencies at which the pump communicates, and with readily available software, the hacker could take over the controls of the pump. The only limitation is range: the attack is limited to the general range of remote control (a couple of meters), but with special equipment, the range can be increased. An attacker could, for instance, target someone who’s inside their home from outside.
It was an app that could kill people, built to prove an important point, and that it did. Maybe due to media pressure, maybe because people finally realized how dangerous this could be, producers issued a voluntary recall, and the FDA issued an official warning.
But it wasn’t possible to completely patch or stop the vulnerability. People didn’t want to return the vulnerable diabetes pumps because it turns out, they were hacking the pumps themselves.
Hacking for good — meet the loopers
They’re called “loopers,” and they take control of their diabetes. Even without any formal training, thousands of patients have hacked their own insulin pumps to create a loop system in which a continuous glucose monitor constantly communicates with the pump itself. This way, instead of manually controlling the pump and adjusting the dosage, all you need is to set up a smartphone app.

More often than not, the sensor and the pump are not directly linked, which means that the patient must constantly read the sensor and adjust their insulin dose. But with a “loop”, that’s done automatically, and it makes the whole thing so much easier. Ironically, loopers use older pumps because the new ones are more difficult to hack.
This is not just some offbeat approach, there’s a big movement behind it. It’s supported by programmers who are developing open software, and even medical professionals, who say that regulatory approval is too slow and inefficient. Dr. Irl B. Hirsch, a professor of medicine at the University of Washington Medical Center, is such an advocate. He says that the looping systems offer “smoother glucose levels than we can get right now with the approved devices.”
The approach is more than just for convenience: people have to constantly dose their own insulin intake based on what the sensor is saying, but for those with no medical knowledge, it can be a daunting task (it’s like a doctor giving you medicine and then asking you to decide the dose yourself). Automated systems do exist, but they’ve only emerged in recent years and can be prohibitively expensive — which is why many are opting for a different option. A new insulin pump tends to cost between 2-3,000 EUR, and the yearly price for consumables can also easily go over 1000 EUR. Looping just makes it all so much cheaper.
It’s experimental, but it’s surprisingly common. The internet is already full of stories of people looping their own pumps. There’s even an uplifting hashtag this loose movement rallies around (#WeAreNotWaiting), and it’s driving producers to make better, cheaper products.
It’s the best and the worst of the IoT movement, all in one story: customizing equipment, hacking it for useful purposes, and the threat of malicious hacking — two sides of the same coin. Within the looper movement, there’s an entire microcosm of the entire Internet of Things: it has the potential to truly revolutionize our day to day life, but it comes with a set of threats. After all, technology is neither good nor bad: it’s how you use it that makes it good or bad.


Hacking and tinkering is at the beginning of many new technologies, especially electronic/digital ones. Early on there were radio amateurs who tinkered with their radios themselves, then of course the PC pioneers who modified/extended their Apple 2 or whatever. Yes, you can even consider Apple founders Steve Jobs and Steve Wozniak as tinkerers and hackers.
And of course this continues now with insulin pumps. By the way, it is not surprising that the official, registered and certified insulin pumps are much more expensive than the older ones with the same functionality but without support for the latest safety standards. It is not uncommon for certifications to make products more expensive, often so much more expensive that the certified standard does not even spread because no one buys it at that price.
Regulations and the wrong standards can put entire technologies out of business. High-speed train lines, for example, cannot be built in the USA (but they can be built in China) because regulations and standards make the technology too expensive in the USA.
This product has been a game-changer for my diabetes journey. From personalized tips to valuable data insights, it’s the ultimate tool for better control. click here to unlock the secret to successful diabetes management!