Encryption has never been more important for — but it’s too often misunderstood
BLOG: Heidelberg Laureate Forum


We’ve never communicated online more than we do now. The world is becoming more and more interconnected, and it’s not just globalization and the ever-growing expansion of the internet — the pandemic has also played a role. Although many are gradually returning to the office, an unprecedented number of people are working from home, which means they’re communicating and sending potentially sensitive information online.
Thankfully, we have encryption.
Nowadays, end-to-end encryption is how most messages are sent around the world, but increasingly, some governments are trying to do away with encryption and ensure they have a way of breaching into messages when it would be deemed necessary. This could help discover and stop acts of terror but it could also make it easier for third parties such as internet providers and even the authorities to snoop in on people’s conversations.
Even ignoring the complex and ethically challenging issues associated with this idea, there are also major technical hurdles that would need to be overcome, and it’s not clear how this would be done.
Encryption 101
Think of it this way: Alice wants to send a letter to Bob, but she fears the mailman will read the letter and she doesn’t want that. So she buys a lockbox with two keys. If she can meet up with Bob somehow and give him one of the keys (because she can’t send it via email, otherwise the mailman can intercept the message), she has ensured a form of end-to-end encryption.
In this simplified example, the two are sharing messages over an unsafe channel, and have devised a way to ensure the privacy of their message. Of course, online encryption is much more complex, and there are several types of encryption.
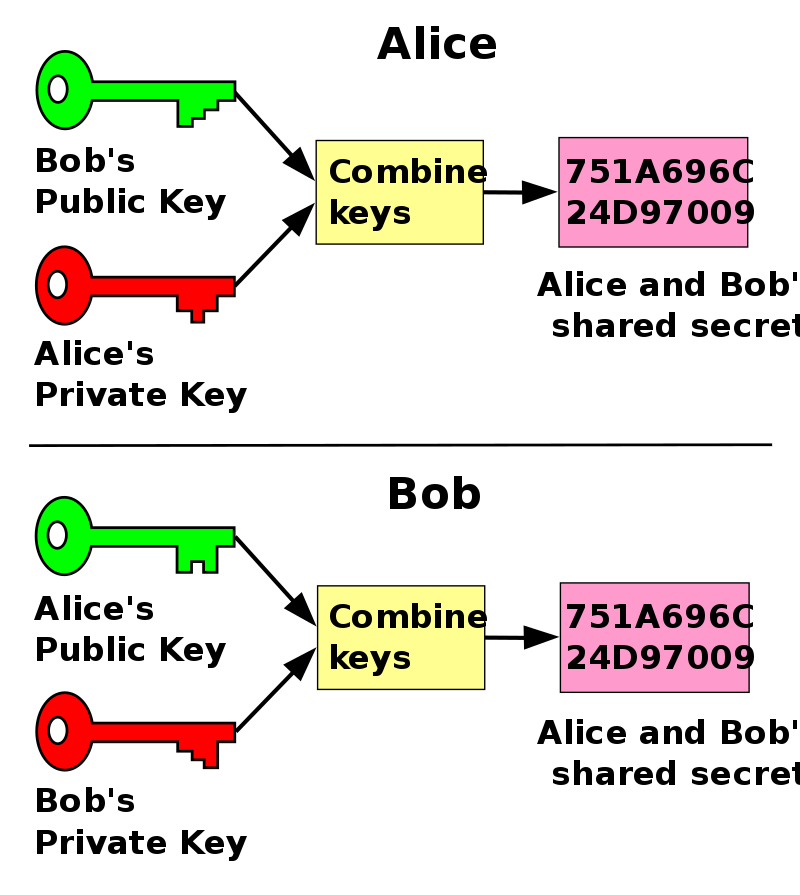
An important form of encryption was also proposed by Whitfield Diffie and Martin Hellman, who received the ACM Turing Award in 2015 and have attended the Heidelberg Laureate Forum. Their work is the backbone of the modern encryption we rely on today.
A struggle for encryption
Governments tend to dislike encryption because they make it harder for them to catch criminals. Users like their privacy, and tech companies like to operate as freely as possible. The tug-and-pull between authorities, companies, and the public is bound to be complex. To make it worse, at least in some instances, authorities have shown a striking disregard for user privacy — or simply a lack of understanding regarding how encryption works.
For instance, in 2017, then UK Home Secretary Amber Rudd called for end-to-end encryption to be banned, claiming “real people” don’t need it. Rudd also wanted to force companies to install a “backdoor” that would offer authorities the possibility of tuning into conversations when it would be deemed necessary. The UK government proposal said, “you don’t even have to touch the encryption” to install something like this — but that’s hardly true.
Several similar proposals (if not in form, at least in spirit) have emerged in the past few years. In the EU, officials have recently called for companies to build ways to break into their own encryption. In India, new rules for messaging services undermine people’s ability to have a private conversation, and in Brazil, the Supreme Court may soon decide whether the government can shut off encrypted messaging services. In China, there is virtually no end-to-end encryption, as the Cryptography Law offers the government full access to all encrypted content and communication companies are required to turn over all user data.
While you could try attempt to justify the ethical implications of these proposals (and that’s a big conversation in itself) the technical challenges are not trivial — and unfortunately, they are too often ignored by officials.
“Rudd’s comment reflected tremendous ignorance about how modern communication works,” noted Dr. Paulo Garcia, Systems and Computer Engineering at Carleton University, Ottawa, in a recent article. “The proposal, referred to informally as ghost protocol, is a more strategic attack on privacy, packaged in security rhetoric that hides technical, personal and societal implications.”
No middle way
When it comes to end-to-end encryption, which is currently the preferred approach of many large online companies, there’s no middle way: it’s either encrypted, and it’s not. If a conversation is truly end-to-end encrypted, the messaging company couldn’t turn over the data even if they wanted to. This is why, increasingly, there is political pressure to undermine or outright ban encryption.
Proposals like Rudd’s (which seem to be gaining more and more traction) would have companies add a new user to encrypted conversations. This “ghost” user (officials) would be able to access the conversation only in legally approved situations, but it would require messaging apps to change how keys are negotiated among participants. This would not just add more complexity to the system, but also more vulnerability.
For instance, it would make it much easier for messaging companies to gain access to users’ conversations (something which is not currently possible with true encryption). Even an employee with enough power would be able to have a peak at conversations.
Furthermore, this would create an important point of failure: should an attacker hack into the messaging app, they could access the ghost user and inject themselves into any conversation. Essentially, ghost protocols would make it so that encrypted conversations are not really encrypted anymore. So contrary to what Rudd claimed, a ghost protocol would involve a lot of changes, and these changes could further jeopardize user privacy.
If one or several countries were to mandate this type of protocol, it’s also not clear how the messaging platform would implement different types of encryption. Would there be two different versions of the platform that work in parallel? What happens when users from countries with different encryption laws want to talk to each other? It’s not clear how these problems (and many more) would be overcome.
Ultimately, the problem of encryption is a very human one, and it can largely be summed in one question: should two people, regardless of where they are in the world, be allowed to have a completely private conversation? People have private in-person conversations all the time, and few would argue against this right, yet somehow, when the conversation takes place online, the matter is much more contentious.


There are many reasons for private communication – most of them legal. For example, companies have trade and business secrets that give them a business advantage over their competitors. Nobody questions that.
More often, governments and court cases do not feel the need to access the encryption until it is determined that the information could be clarifying. One solution for everyone involved could be for a sender of encrypted information to store the encryption key in a special container that can only be opened by a user key and a government key and only a court judgment would allow access to these keys.
I do not believe this.
Competent criminals will have no problems to find ways to transfer their data which will not be catched by backdoors etc. Think about hiding the relevant information in Texts or images (Steganography).
That means that criminals or terrorists are not affected by forbidding encryption or adding backdoors to encryption methods.
It is even worse, every backdoor the government installs can be used by criminals as well.
So what is the real cause for such ideas?
I see two possible answers:
1. Incompetent politicians who have no clue about what they are talking. Think of “the internet is virgin soil” .. as Merkel said 2013 … well the internet is technology from 1969 .. I hope she has no problems using her smartphone which is much younger. (maybe she is even thinking that this is the same). Of course the mathematics of encryption are even older.
2. Politicians who want to control their people. Of course those politicians can use the ones from 1 for their ambitions.
Encryption does not make it harder to catch criminals. This is a very common, but nevertheless basically unfounded misconception. Encryption will not depredate Police authorities of any opportunities, which they had in former, encryption-less times.
But modern communication services, combined with encryption, allows criminals, to operate on a much more interregional resp. international level. This services give criminals opportunities, which they historically never had.
So modern communications enforce police authorities to adapt their methods to modern times (e. g. the notorious german Quellentelekommunikationsüberwachungsverordnung resp. the most current Quellentelekommunikationsüberwachungsverordnungnovellenentwurfsvorlage). Of course, it would be much simpler for them, if they could eavesdrop all communications – not only that of criminals, but of each and every person.
As it was be much easier to investigate, when they simply could cudgel down, torture or beat up any potential suspect – back in the good old times. Would make their work much easier – but is unfortunately no longer common in most parts of the world.
It truly is heartbreaking to see hardboiled policemen weeping, crying, moaning over their opportunities lost through encryption – but it’s a hyena’s weeping. The tears they shed are the tears, the wolf shed’s over the sheep he can’t eat, because he’s already stuffed to the upper lip.
Amber Rudd‘s Desire: Scan the whole internet to be informed
Amber Rudd’s proposal to make encrypted data readable for the “government” ultimately boils down to maintaining the state that existed before Edward Snowdon cleared up the Global Surveillance and Espionage Affair in 2013: namely a state in which Secret services were able to search almost all Internet traffic for interesting reports.
For the espionage services it is of course best if the people who communicate with one another do so without any inhibitions, in the opinion that they are exchanging information unsupervised – when in reality it is the other way around.
Of course, there is a need for a state and a secret service to know what is going on in their own country, even in the whole world, because some of it could be of state interest, and some of the information that could be obtained in this way could even be of vital interest to a country being.
I think private individuals should not be under any illusions about the privacy guaranteed by the state: there may be this on paper, but in practice the intelligence services will try again and again to undermine this privacy. It still applies: if you really want to keep things secret, you should rely on your own means of secrecy and not trust state / public means.